Internet Security Fundamentals - Online Edition
13 Smartphones & Tablets - part 2
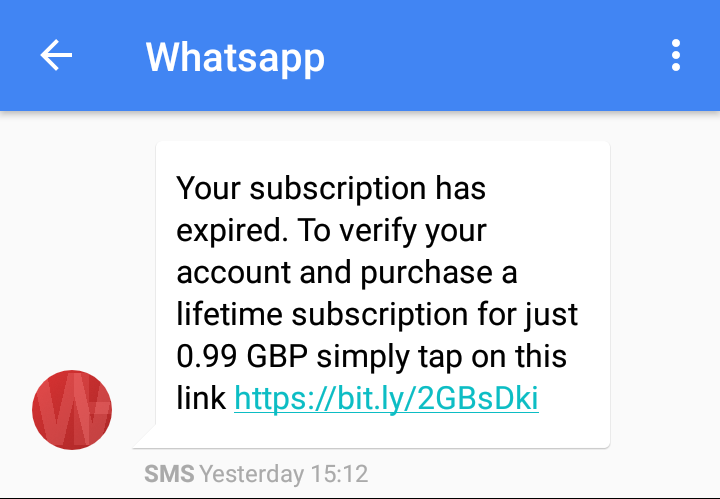
In the following example a text message is claiming to be from WhatsApp and that my subscription has expired. It then goes on to say that you need to verify your account and offers a special deal of a lifetime subscription for 99p by clicking on the shortened bit.ly web link. Here the criminals are relying the fact not everyone would realise that WhatsApp is now completely free, together with the smaller mobile screen size to hide the look-a-like web domain of vvhats-app.co.uk, where two v’s would hopefully look like a w on a mobile screen. Straight away they ask for your name, address, date of birth and contact details, they then ask for a debit or credit card and bank account details.
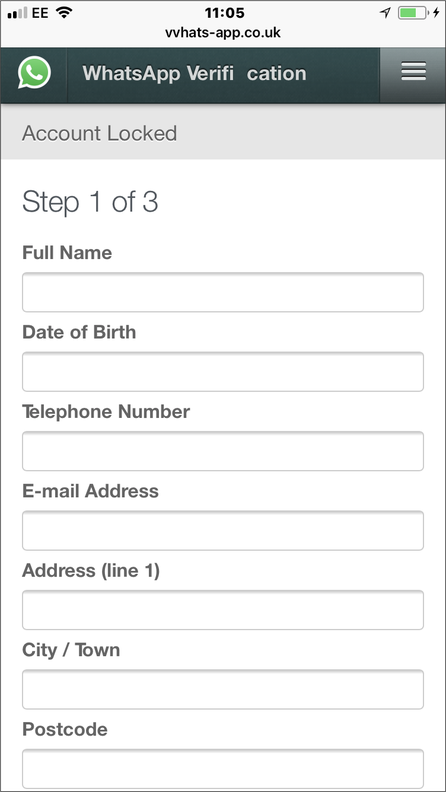
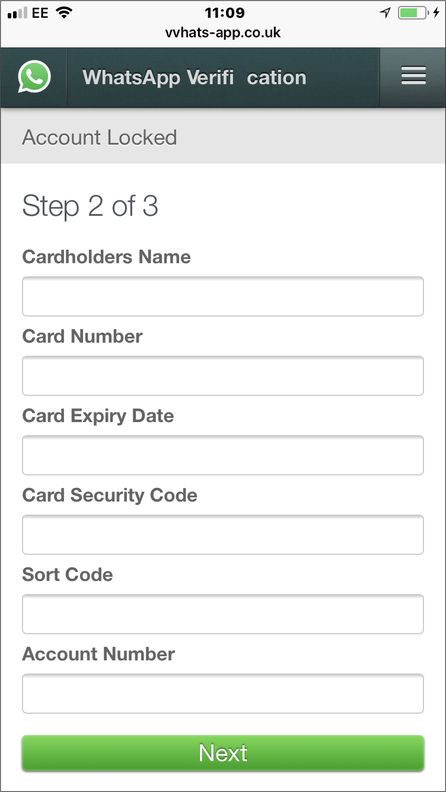
Step 3 of 3 goes on to ask for a Security Question, giving you the choice of Mother’s Maiden Name, Passport Number or Driving License Number, basically everything needed for ID theft.
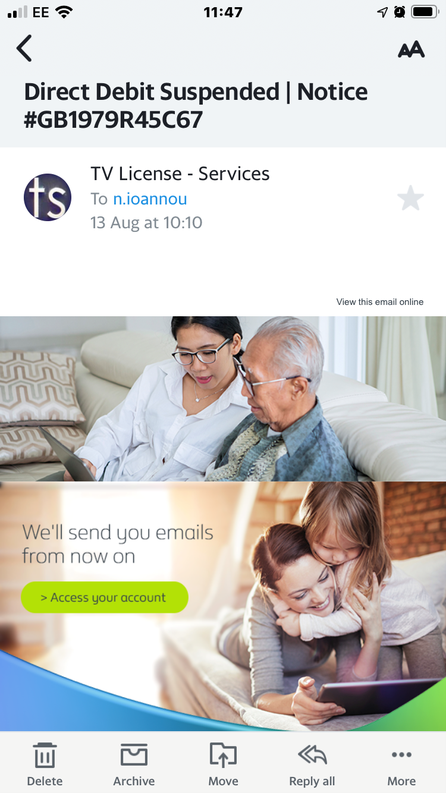
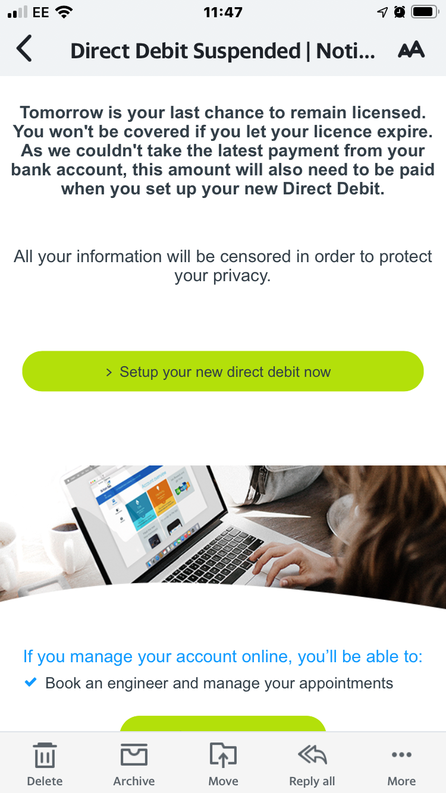
Another trick the criminals use to get all your bank account details and personal information is the fake ‘your direct debit has been suspended’ email alert. There are a number of payments people must make annually, like income tax, but in the UK, we also have an annual TV license per household which carries a large fine if not paid, so a lot of people take advantage of the smaller multiple direct debit payments option. So, here we have a perfect example of a nearly universal tax/bill that many people pay by direct debit and failure to do so could result in a hefty fine. The hook, carrot and stick already created for the criminals to base their fake mobile centric email campaigns, like this one below:
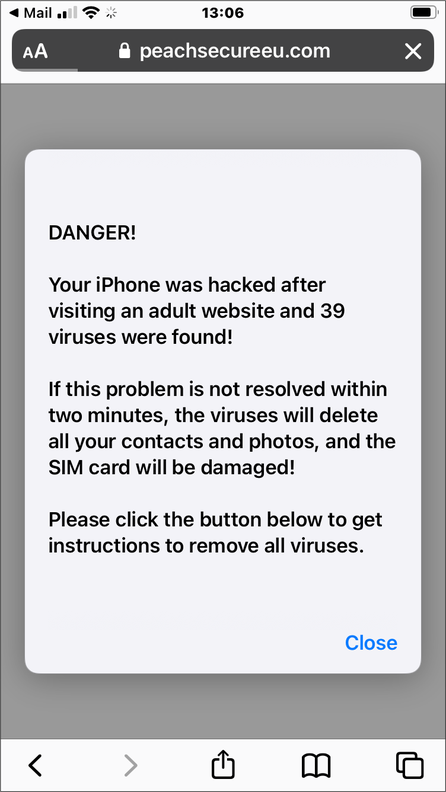
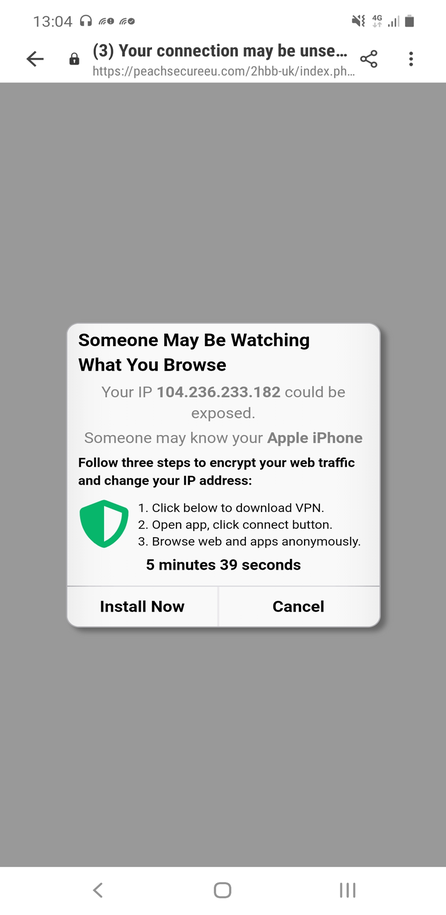
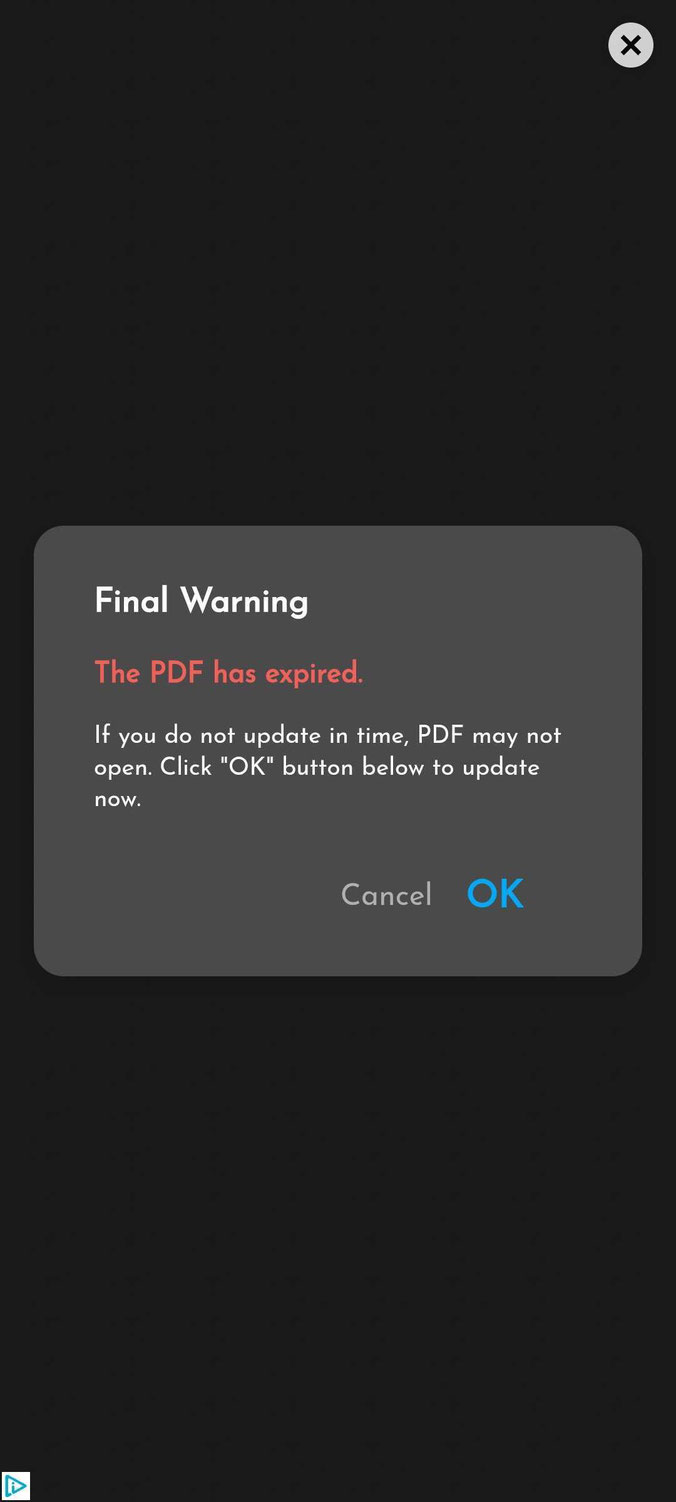
Another trick cybercriminals use is to make a website look like a mobile phone system alert dialog, warning you that you have been compromised or that your device has been infected with a virus or even multiple viruses. Here the goal is to get you to install an app and for verification your account credentials (which is often the real goal), or to trick you into buying an overly expensive app (often a Virtual Private Network or VPN app with a high monthly subscription) which is defined as ‘fleeceware’ in the glossary of this book. The original website link source is often a SMS text message or mobile phone based social message, rather than an email, as this scam only works if viewed on a mobile phone.
The following two images are examples of the same fake link aimed at iPhone users, the first image is on an iPhone, while the second is on an Android phone, displaying different content (though still mentioning an iPhone).
Unfortunately, there are now new ways that you can be scammed and charged while surfing on your smartphone. Recently one of my colleagues was internet surfing on his smartphone to pass the time while in a doctor’s waiting room. They clicked an advert from a mainstream website and answered some questions on a really easy quiz. Soon afterwards a SMS text message arrived informing them that they had just been charged £30 as there was a £6 charge for each question. Unfortunately, the advert had been placed in between some just for fun questions from the main website, which my colleague was just working their way through. They didn’t read the small print and clicked the answers, but at no point was my colleague asked to confirm payment, no ID of any kind is requested.
They were charged using a system called Payforit Single Click, a legitimate service which the mobile phone networks have adopted to make instant payments. So be careful when surfing on a mobile because you can now be charged just for clicking something. It might be to view a video, submit an answer or download a document. If you can try to ask your mobile phone provider if you can opt out of premium services or Payforit (ask for a MPAY bar) and set up a spend threshold alert. Also having the mobile phone provider’s adult content filter turned on will also help block some of the websites that use these instant payments, so check with customer service in case you’ve requested it to be turned off in the past. Keep an eye out for a website banner like the one below, which shows that you are agreeing to be charged. Either way, be extra vigilant when browsing the internet on your smartphone, otherwise you could be in for a nasty shock when your mobile phone bill arrives.

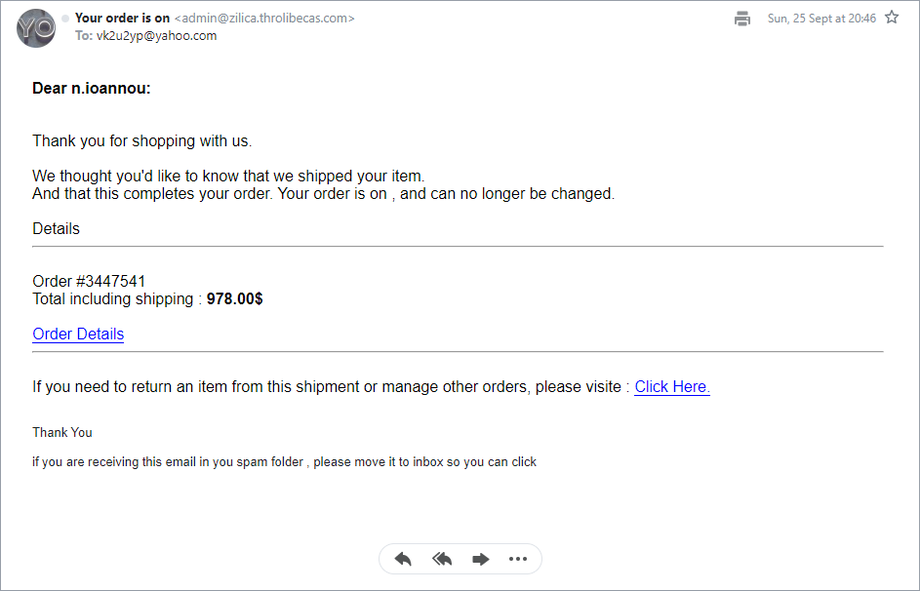
Another area you need to watch out for is the fake app purchase confirmation email. In the example below a high-cost app has supposedly been downloaded, but if it was a mistake you can click the ‘Cancellation Form’ link. Notice how there is no £ or $ sign as well as a range of typos. Clicking the cancellation link may take you to a fake login page where they hope to capture your username and password for your Apple or Android account, or take you to a website loaded with an exploit kit to silently install a virus or Trojan.
From: AppStore [mailto:isto@isapp.net]
Sent: 21 August 2015 19:12
To: Nick Ioannou <nick.ioannou>
Subject: Your recipt No. 2183124194
Your AppID was just used to download GPS Toolbox from the AppStore on a computer or device that had not previously been associated with that AppID.
Order ID Number: PIE93UD9END8DJ
Order total: 49.00
If you initiated this download, you can disregard this email. It was only sent to alert you in case you did not initiate the download yourself.
If you did not initiate this download, we recommend that you go to Cancellation Form to cancel this order.
If you receive an app purchase confirmation, you can check from your device or via a computer. From an Apple device open the App Store, select Updates, then Purchased or visit reportaproblem.apple.com which will list all your recent purchases. For Android devices, open the Google Play Store app, touch the Menu icon and select My account.
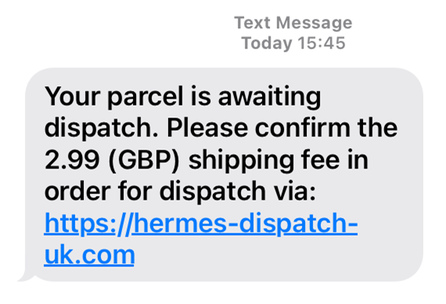
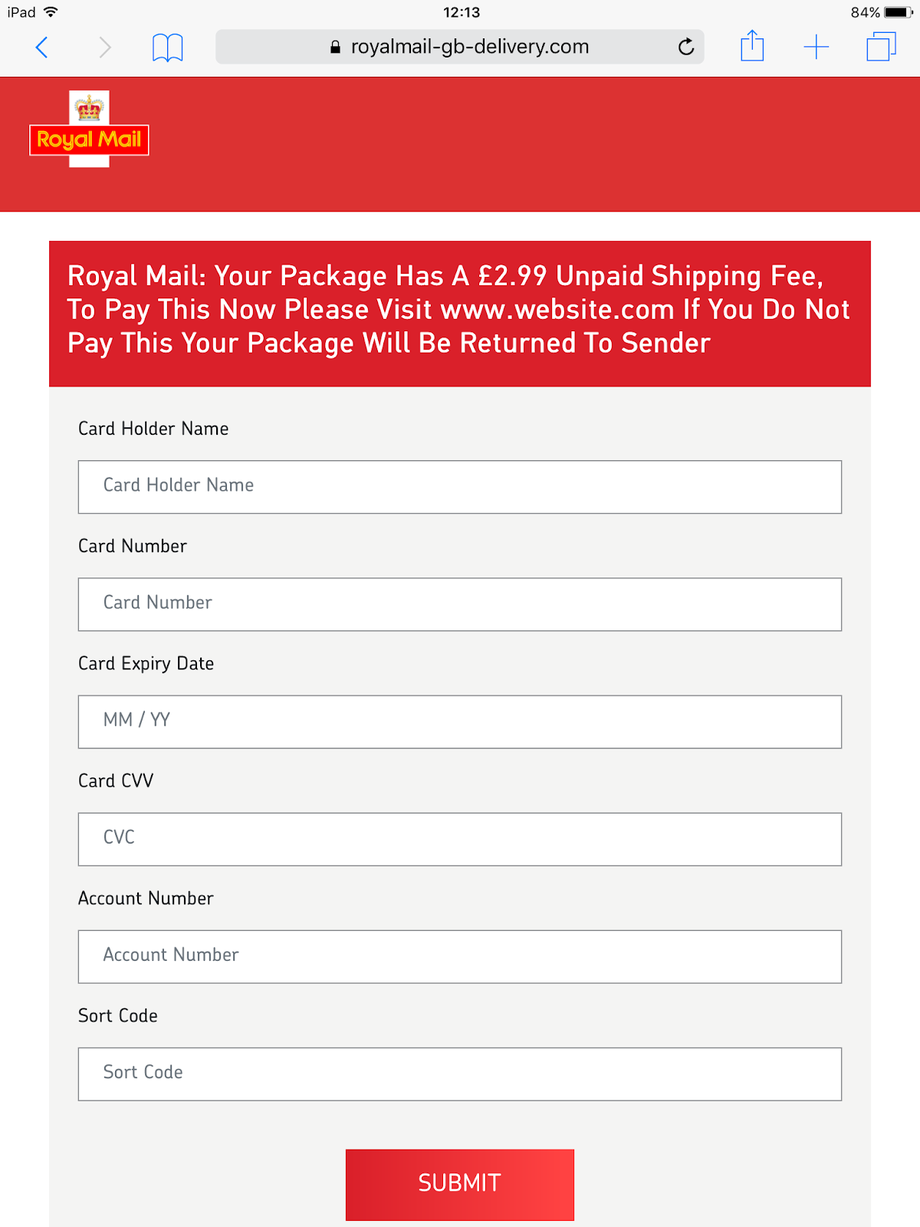
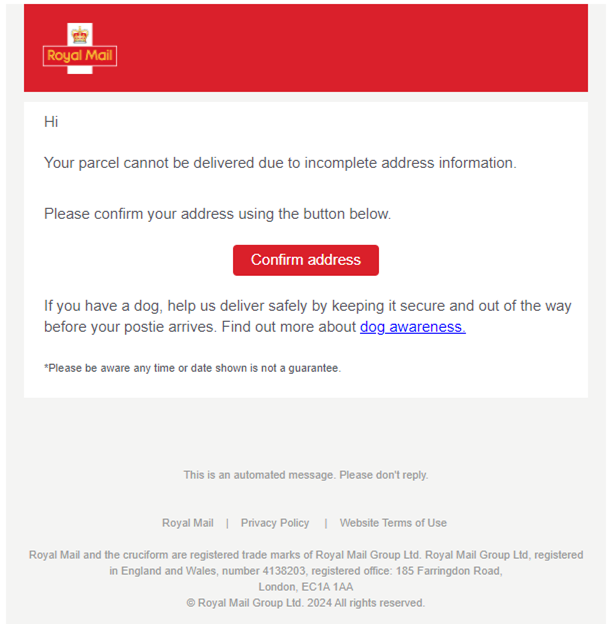
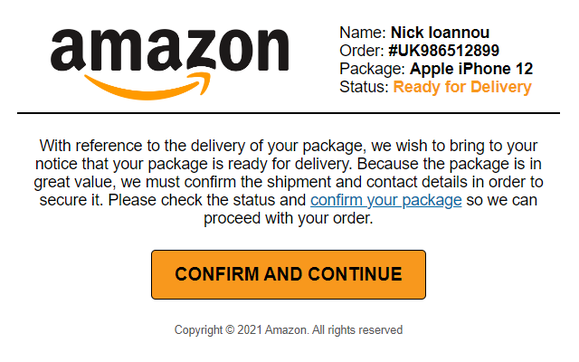
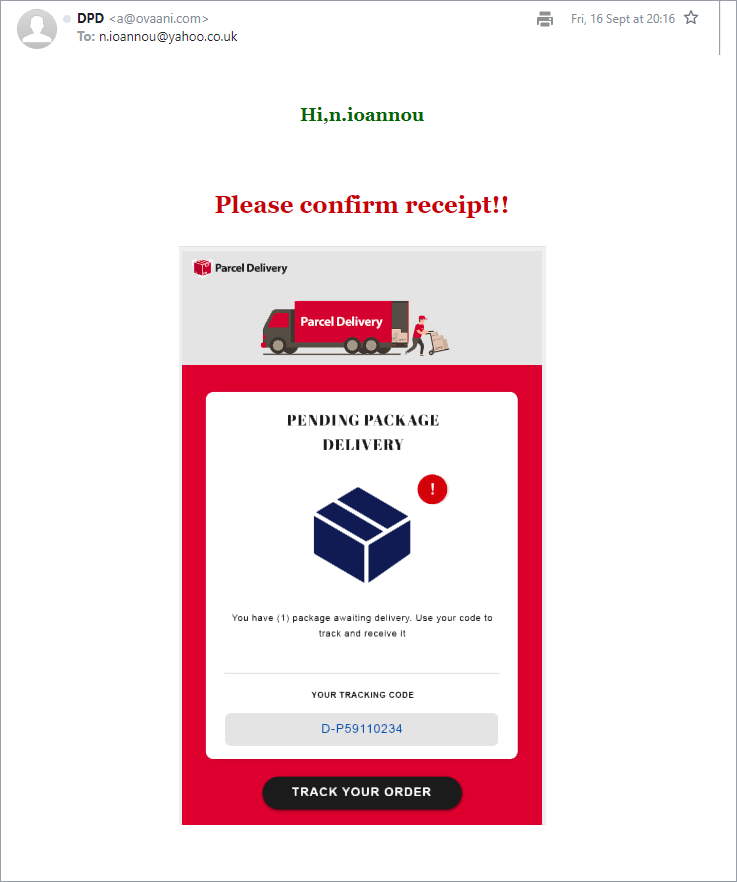
With a large number of people now working from home, there has been a large rise in fake courier and postal service SMS text messages. Typically, they say that there is a problem with a delivery, a delivery was missed or that a small fee needs to be paid. These point to fake web domains that contain the name of the service and most of the time, seem perfectly plausible.
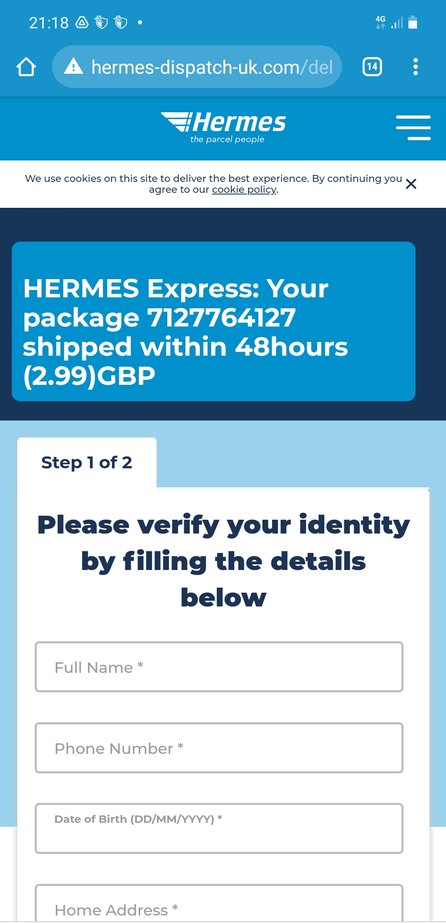
Here’s an example of a typical text message claiming to be from the courier Hermes. The link seems perfectly plausible and looks the part. The giveaway for most people is the date of birth field in the verify your identity.
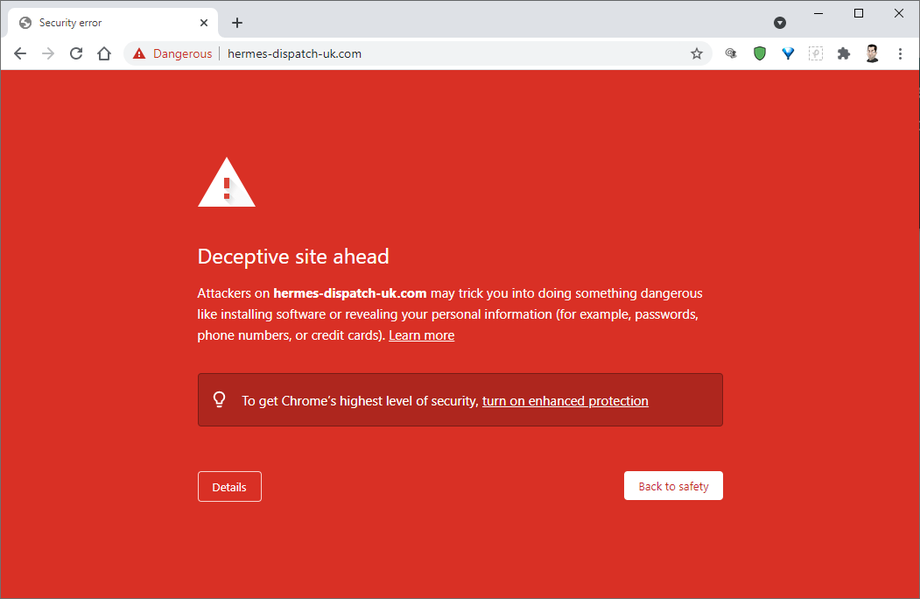
Now things look a lot different if you try to open that same link in a desktop browser, chances are a modern web browser, or your antivirus software will block the attempt to visit the fraudulent website. In some cases, the website checks to see whether you are using a mobile and if not, sends you to a legitimate page, in order to try and fool you.
Most people think that it would not be easy or even possible for fraudsters to purchase web domains containing brand names of major companies, but with so many domain name combinations being purchased daily in the hundreds, the opposite is true.
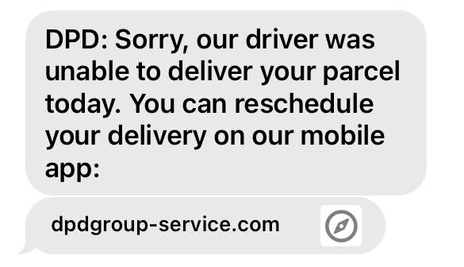
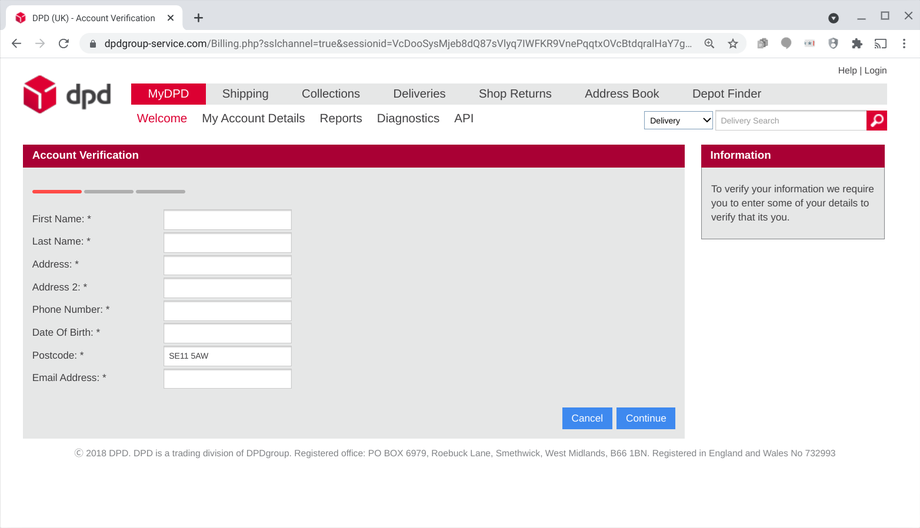
Here's another text message claiming to be from the courier DPD. Once again, the web link seems more than plausible, and if the fraudsters spoof the official text message number, the fake website message could be in a list with real messages from that courier.
Following the link took you a perfect copy of the DPD website asking for a name and postcode. Every menu button worked, instantaneously taking you to the real DPD website, they just hoped you clicked the back button, to return to the fake version. In order to see what happened, I entered the name ‘Smith’ and the postcode of the MI5 Security Service building in London.
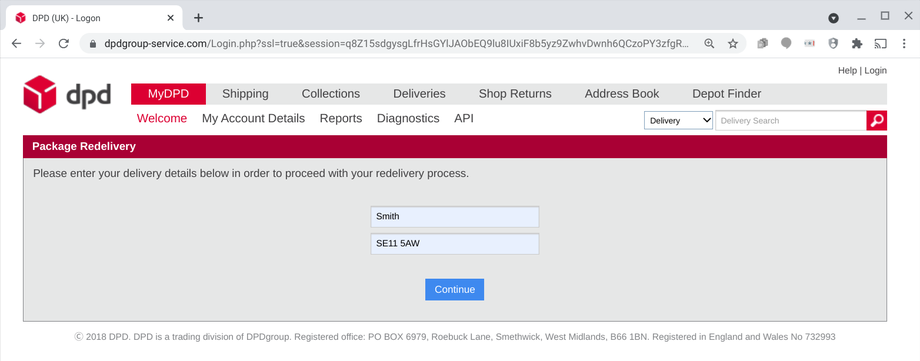
It didn’t really matter what was entered, as the second page asked everything the fraudster needed, before moving on to payment information. If you think you may have been tricked by one of these fraudulent messages, please contact your bank immediately.
Couriers and postal services are great candidates for these types of scams, with more and more people ordering goods online, combined with many more people working from home, missing a delivery is a common place occurrence. If you receive a similar message and are not sure if it is real or fake, visit the website of the reseller you are expecting a delivery from and request the courier tracking code. If are not expecting a delivery, ignore the link in the message and search for the official website of the named courier service, to contact them to verify the message.
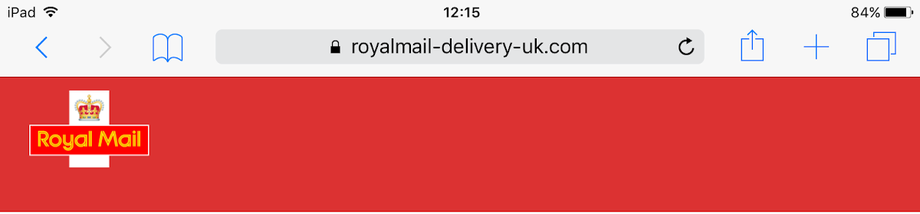
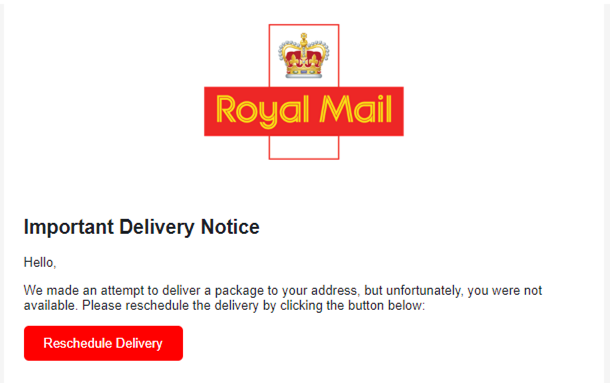
Here are a few more fraudulent web domains for Royal Mail in the UK.
This one is https://royalmail.deliveryconfirmation-id.com
While this one is https://royalmail.mypackageupdates-id.com
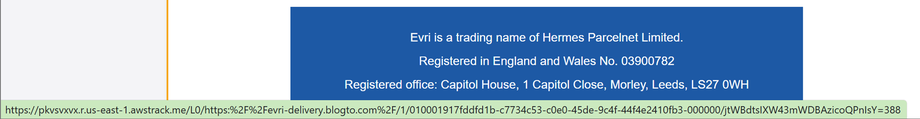
Here is another fake delivery email from noreply@freightgpt.com using the gpt ending to associate it with ChatGPT to appear more official. If you decide to verify any suspicious emails on a desktop or laptop, carefully view them without clicking any links) and know that hovering over a button may display something completely different to the destination address.
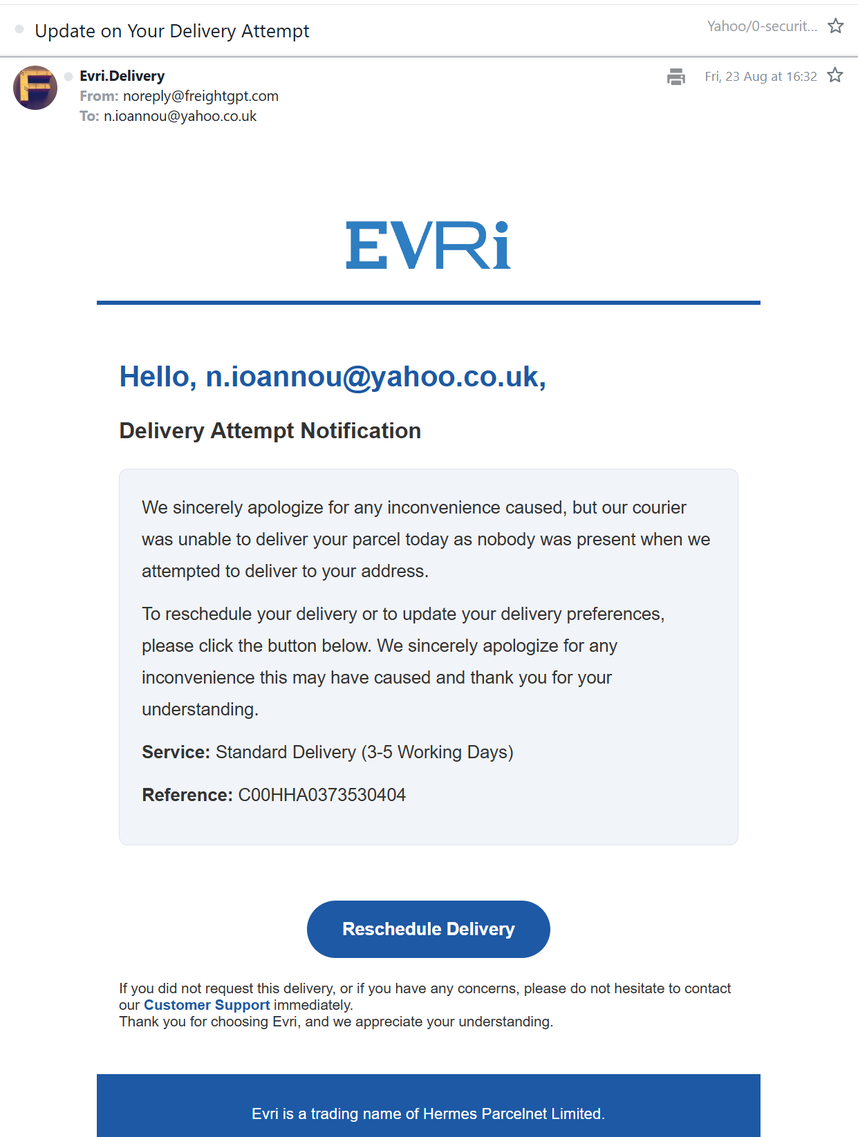
Always check the link address by what is displayed in the bottom left of a desktop browser.
In the UK the National Cyber Security Centre (NCSC has taken down close to 10 million malicious domains over the past seven years, but the criminals spin up new plausible sounding domains as fast as they are taken down. So you don’t get caught out, here is a list of the official UK websites of the major courier companies:
- https://www.dhl.com
- https://direct.tnt.co.uk
- https://www.fedex.com
- https://www.dpd.co.uk
- https://www.evri.com
- https://www.hermesworld.com
- https://www.parcelforce.com
- https://www.parcelmonkey.co.uk
- https://www.royalmail.com
- https://www.ups.com
- https://www.yodel.co.uk
Please create a list for your own country and keep it handy. Remember, subdomains may be valid if they have the full stop before the valid domain name, for example https://about.ups.com is a valid subdomain, but https://about-ups.com is not. Please note, this applies to any website domain, not just couriers.
Here are a few more examples of fake courier emails:
Moving on, your mobile device’s app store is also a very lucrative way of signing you up for a recurring subscription and the criminals know this too. So much so, they have created mundane apps with a free trial, linked to ridiculously priced automatic subscriptions that can cost thousands. Though it is not just about hoping to catch people out that forget to unsubscribe, these apps use typography and graphics to mislead and hide their true nature. The criminals are also using a sneaky trick on Apple iPhones with TouchID enabled. By unexpectedly showing a payment prompt and knowing that people will instinctively press the home button to exit the app, except pressing the home button instead confirms payment. If you see any unexpected demands for payments, make sure to press the power button instead of the home button.
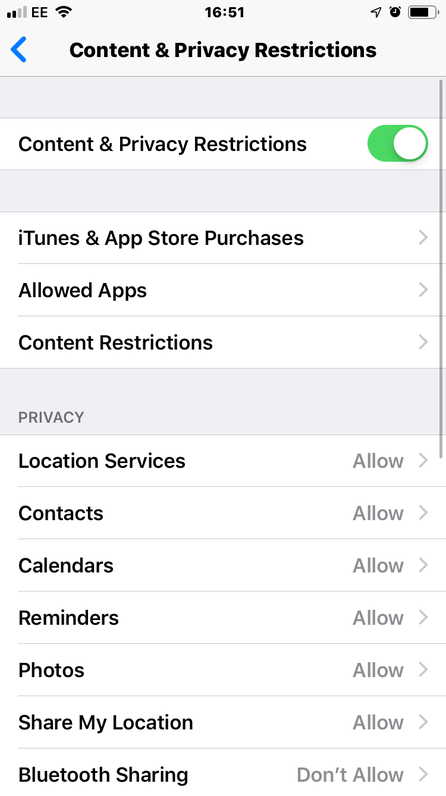
Apple has pulled many of these apps from their App Store, but only with the condition that the apps are clearer about their subscription costs. They have not banned anyone creating a £100 a month subscription ringtone customisation app or a £10 a month calculator. The best way to protect yourself is to disable any in-app purchasing functionality. In Apple iOS, this can be found in Settings - Screen Time - Content & Privacy Restrictions - Content & Privacy Restrictions - iTunes & App Store Purchases.
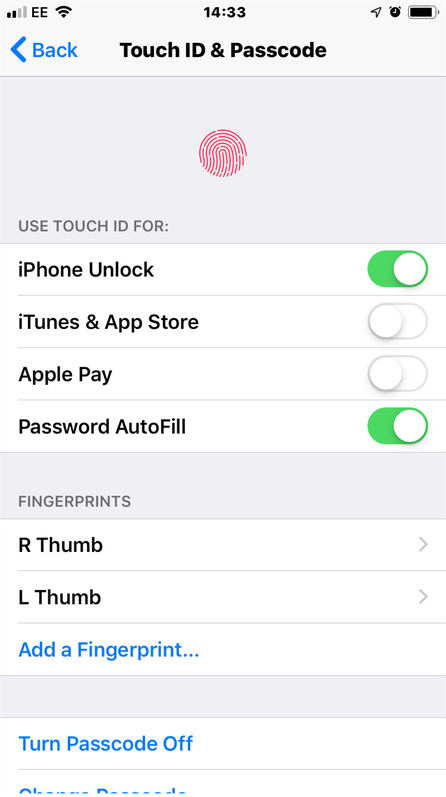
It is also worth turning off Touch ID for the App Store and possibly Apple Pay (especially if you rarely use it) via Settings - Touch ID & Passcode. For Android, you cannot actually disable in-app purchases, only force authentication via Play Store - Settings - Purchase verification – Verification frequency - Always. Be vigilant when installing new apps, otherwise they may end up costing you more than the device you are using them on did.
There has been a trend for cybercriminals to create mobile apps that behind the scenes use your mobile data connection to carry out click fraud, where your mobile generates pay-per-click (PPC) revenue from online adverts. These apps are often useful utilities that you install and then forget about or even games, and while they are not malicious to you, they could cost you money if you go over your monthly data allowance and as well as generally slowing down your smartphone.
QR Codes
One aspect of modern daily life often seen in places like restaurants, car parks and ticket machines is the move to cashless ordering and payments, which has been greatly facilitated by the use of QR codes (Quick Response codes) removing the need to type a long website address into your mobile device.
Despite appearances, QR codes are not new, they were invented back in 1994 by a Japanese automotive company to track vehicles during manufacturing, and over time their use expanded as a more convenient way for smartphones to open a browser to a specific website. The look and feel of QR codes can also vary greatly, for example here are three QR codes that point to my website www.booleanlogical.com

Criminals also saw the opportunity that QR codes presented for tricking people into visiting fake websites without realising, known as quishing, in much the same way link shorteners can hide the destination. As a result, fake QR codes can be found stuck over genuine ones in car parks, restaurants, cafes, and posters, just to name a few locations. Please be wary of any QR codes that could be (or are) stickers, instead look for the full web address or company parking app and enter manually.
Another more elegant way the criminals can doctor QR codes is by supplying you with their free QR scanner apps that they submit into legitimate app stores. This way any genuine QR codes can be made to go to their fake website clones without the need for someone to place stickers anywhere. It is important to note that scanning a QR code is now a feature that is built-in to the Apple iOS and Google Android default camera apps. Previously Android mobile did need a third-party QR scanner app, but this is no longer the case, so please consider deleting any QR scanner apps that you may have installed. Instead, only use the built-in QR code scanners found in Apple iOS and Google Android default camera apps.
- For Apple, see: https://support.apple.com/en-gb/guide/iphone/iphe8bda8762/ios
- For Android, see: https://www.android.com/articles/how-do-you-scan-qr-codes-on-android/
If you do wish to use a third-party app, try Google Lens which also handles QR codes:
- For Apple, see: https://apps.apple.com/app/id284815942?ct=p-pmm-web-Lensmktg-Lens&mt=8&pt=9008
- For Android, see: https://play.google.com/store/search?q=google%20lens&c=apps&gl=US
Or use a scanner from an antivirus company like the Trend Micro QR Scanner: https://news.trendmicro.com/2018/06/18/scan-qr-codes-safely-with-the-trend-micro-qr-scanner/
Fake apps and fake warnings are still constantly plaguing smartphone users, so try not collect app just because they are free. Any app can be updated to be malicious if those behind it are criminals, so be wary of any app permission changes to access unnecessary features like your emails and cloud storage, when it’s just a basic app like a calculator.
Despite everything in this chapter, one of the biggest issues with smartphones is still having them stolen or just losing them, especially as many people use their mobile as the second part of a two-factor authentication login process where a code is sent via SMS to their mobile. So, make sure that your device is backed up and you have your device PIN or pattern lock enabled.
When it comes to choosing a PIN code, try not to use any of these common codes:
| Four-digit PINs | Six-digit PINs | ||
| 0000 | 1998 | 000000 | 159753 |
| 0852 | 222 | 111111 | 654321 |
| 1010 | 2580 | 112233 | 666666 |
| 1111 | 4321 | 121212 | 789456 |
| 1212 | 5555 | 123123 | |
| 1234 | 5683 | 123456 | |
Also avoid using your birth year as a PIN code. If your phone is also your only camera and photo album, make sure that your photos are saved to a cloud backup service so that losing your phone is not a major loss. Lastly, if you have a ‘find my phone’ location tracking feature enabled, make sure it cannot be disabled without a PIN number.
Your smartphone is a portable computer that many of us use every day for sometimes up to five years. Just remember that cyber threats are not the only problems you may encounter during this time. Expect your smartphone to either stop working (water is normally involved) or go missing and plan for this event, so if it does happen, it won’t be a crisis.
Index or next chapter eBay & PayPal


